Chapter 1 Introduction Copyright © The McGraw-Hill Companies, Inc. Permission required for reproduction or display. 1.# - ppt download

Assignment1.docx - 1 Consider a desktop publishing system used to produce documents for various organizations a Given an example of a type of | Course Hero

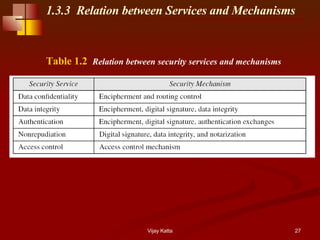
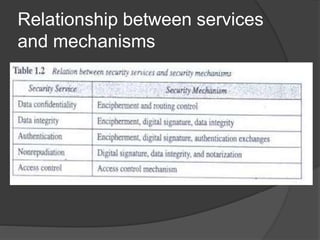
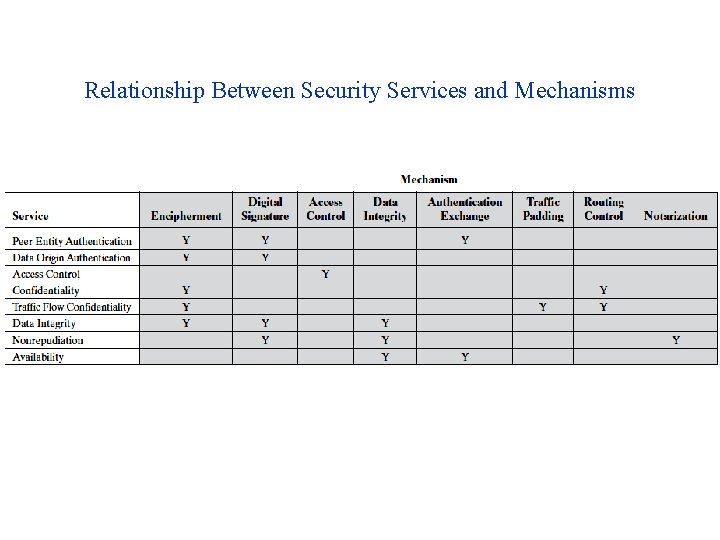
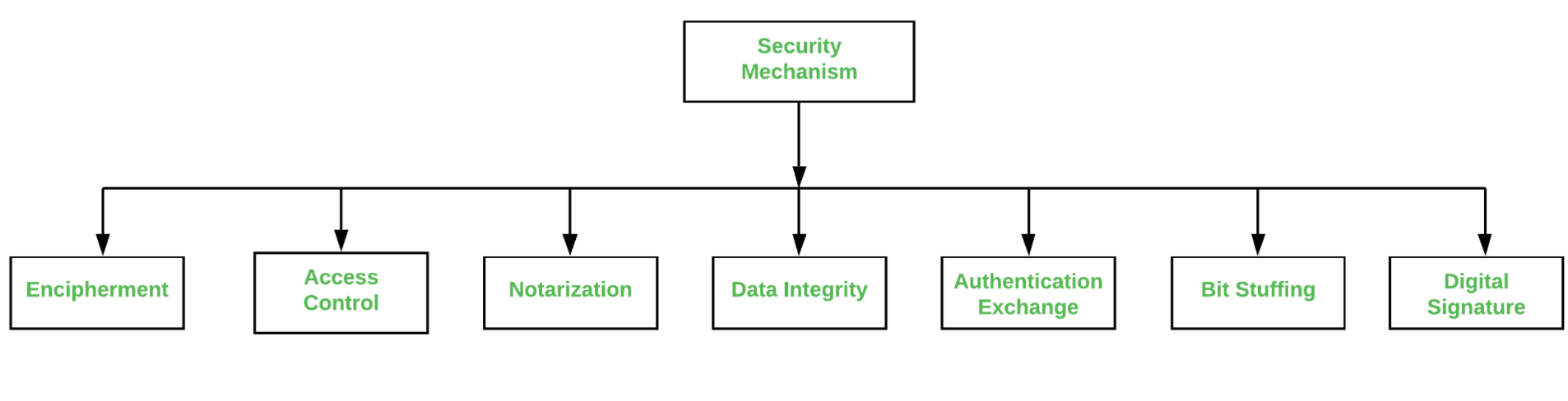
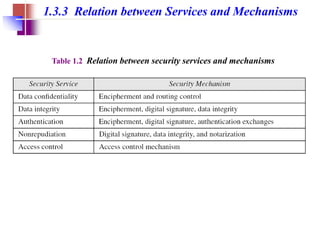
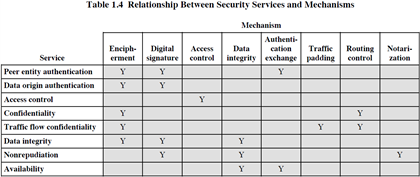
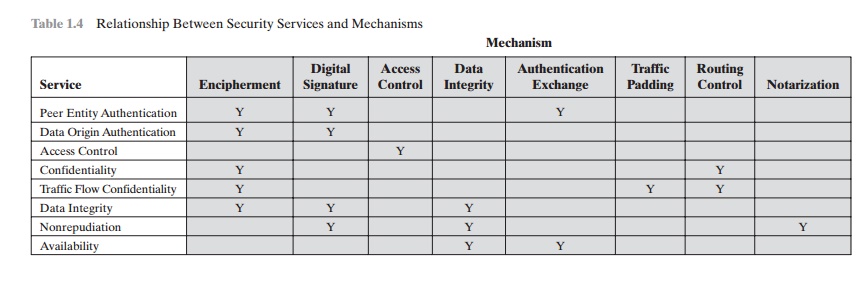
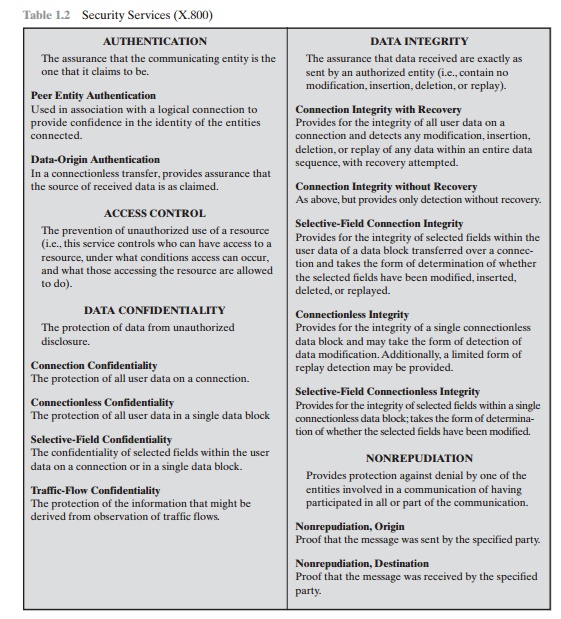
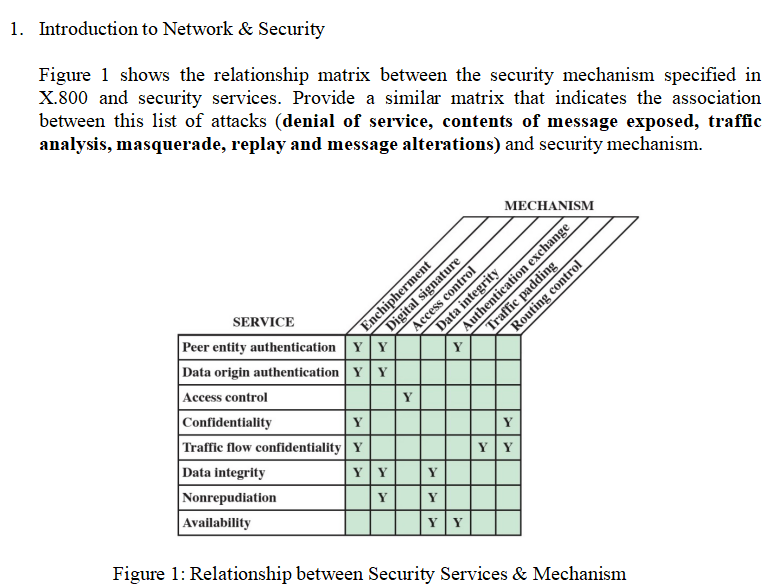
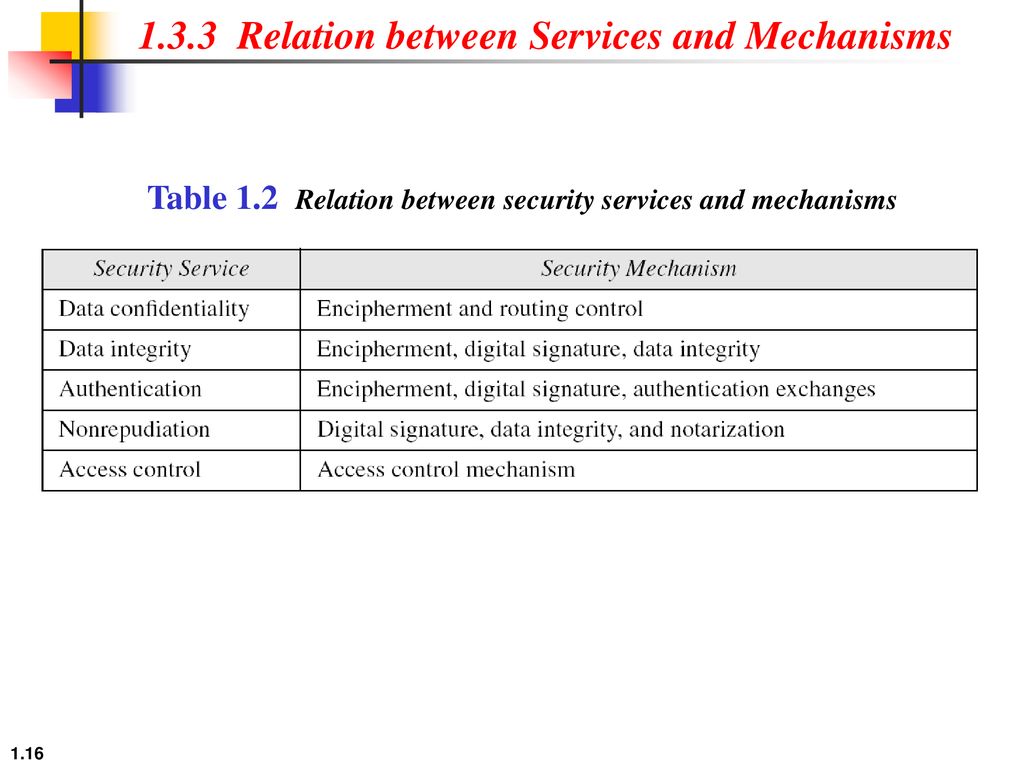
CryptographyBhutan - Lesson 12 #securitymechanism #securityservices Security services are implemented by a security mechanism or combination of mechanisms: 1. Peer entity authentication service can be implemented by or combination of Encipherment, Digital
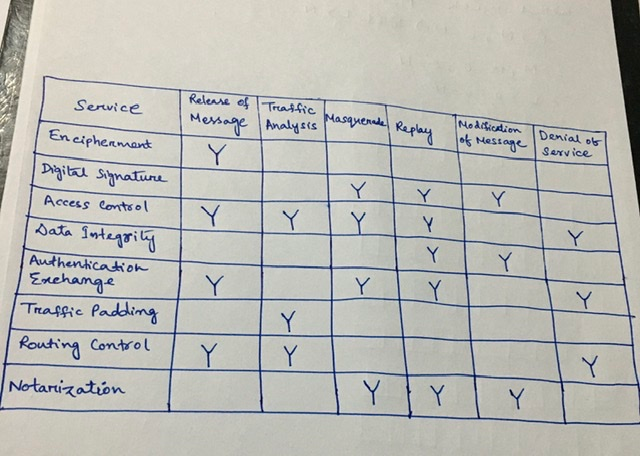
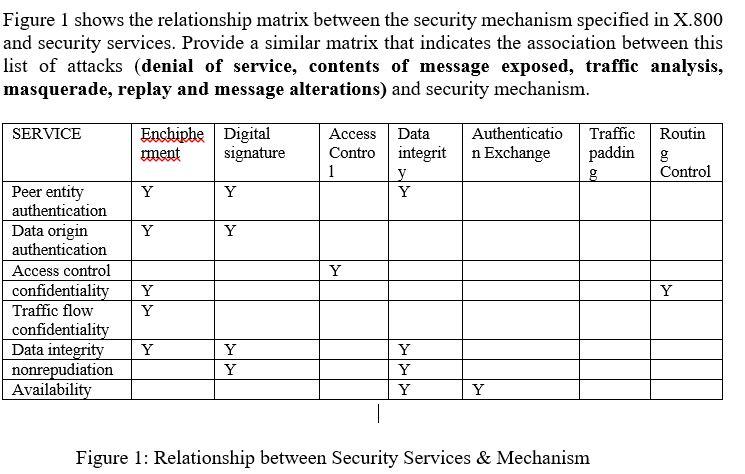
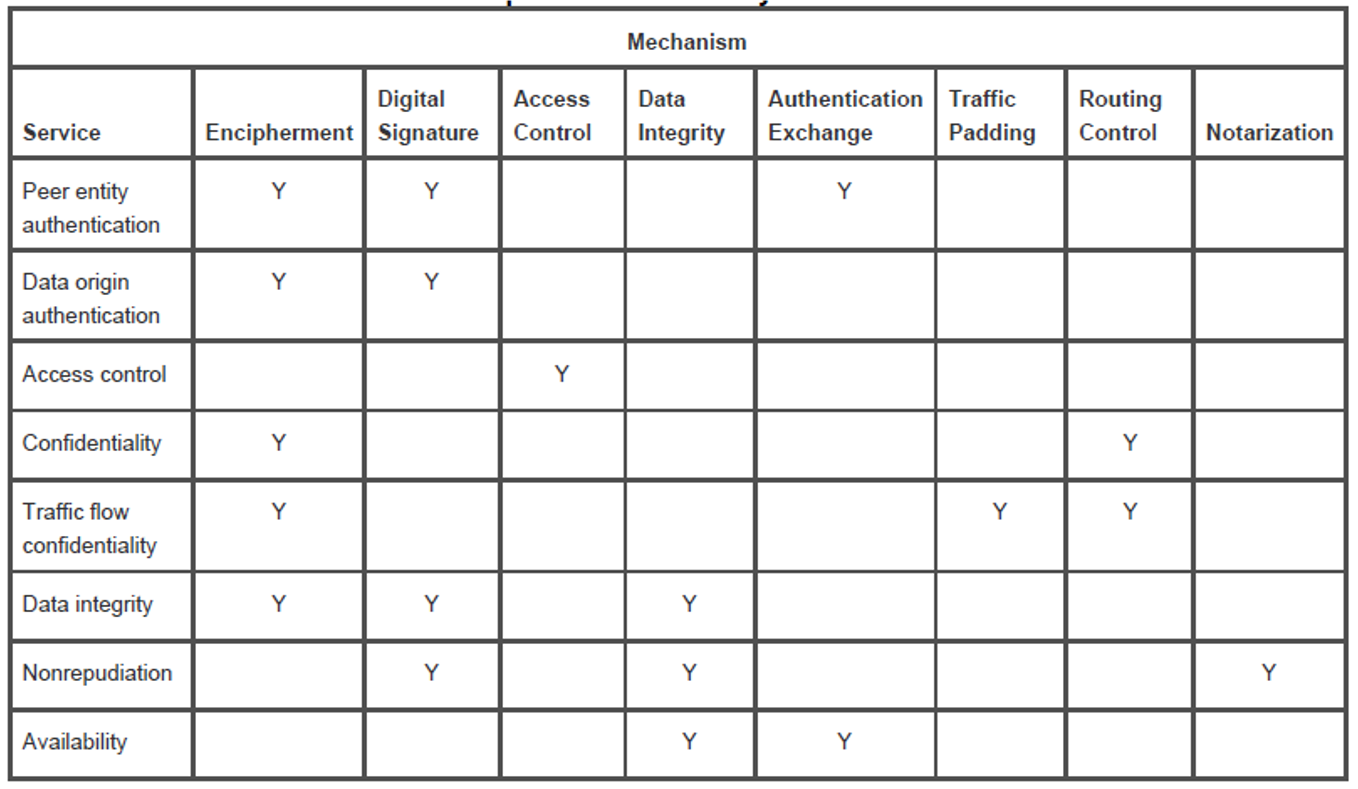
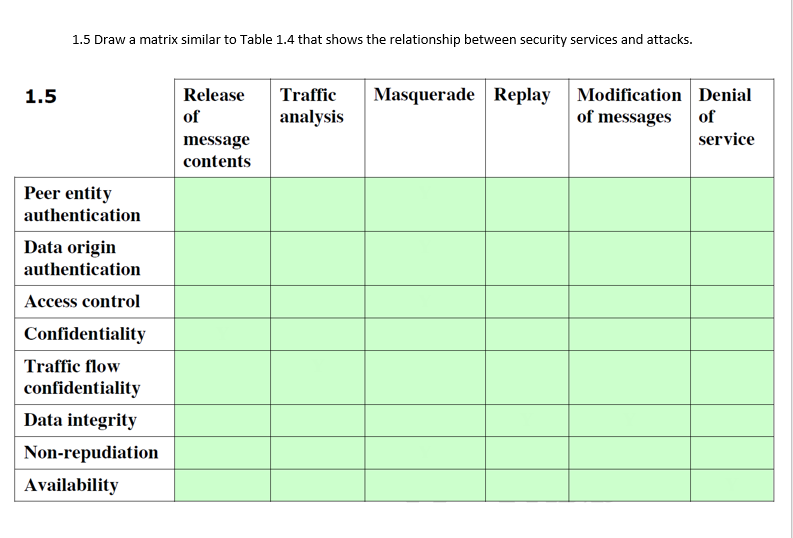
Solved) : Draw Matrix Similar Table 14 Shows Relationship Security Mechanisms Attacks Q42415984 . . . • CourseHigh Grades
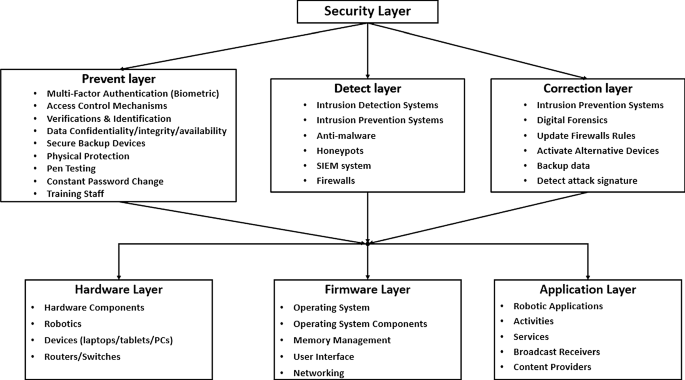
Robotics cyber security: vulnerabilities, attacks, countermeasures, and recommendations | SpringerLink